KelpDAO $292 Million Exploit: Arbitrum Freezes $71M in Stolen ETH as Lazarus Group Blamed
Published: April 21, 2026 | Category: Crypto News | Reading time: ~9 min
Breaking: The Largest DeFi Hack of 2026
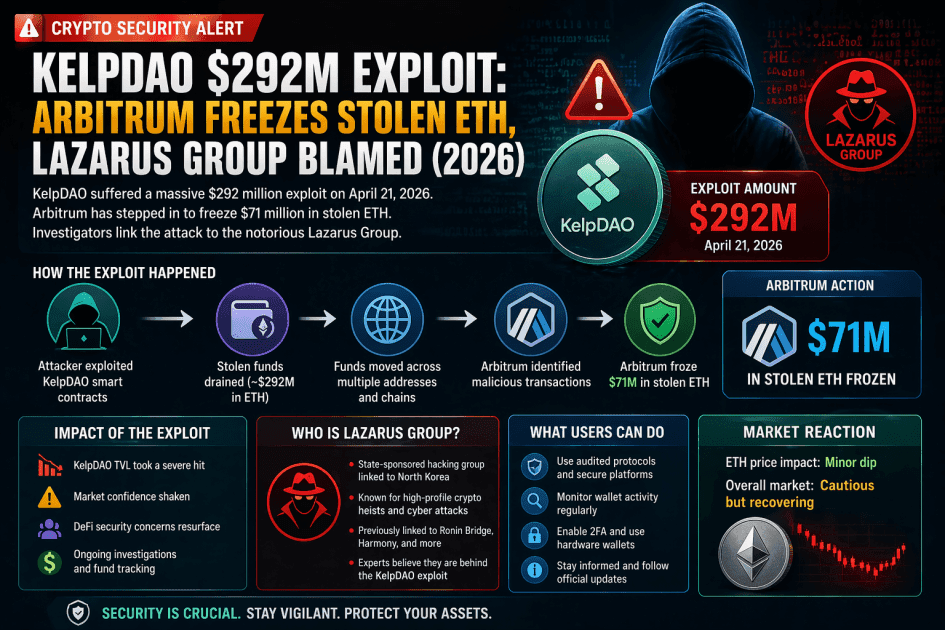
The decentralized finance (DeFi) world is reeling from its biggest security breach of the year. On April 18, 2026, KelpDAO — a liquid restaking protocol built on Ethereum's staking infrastructure — was drained of approximately $292 million in rsETH tokens through its LayerZero-powered cross-chain bridge. Just days later, on April 21, Arbitrum's Security Council took emergency action to freeze 30,766 ETH worth roughly $71 million linked to the attacker's on-chain wallet address.
The attack is now being attributed with preliminary confidence to North Korea's Lazarus Group, specifically the TraderTraitor subunit — the same state-sponsored hacking unit linked to the $285 million Drift Protocol exploit just 17 days earlier. Altogether, a single North Korean cyber unit has drained over $575 million from DeFi in 18 days.
This blog post covers everything: how the exploit worked, the growing blame war between KelpDAO and LayerZero, Arbitrum's historic freeze, the Aave contagion risk, and what all of this means for the future of DeFi security.
What Is KelpDAO and rsETH?
Before diving into the attack mechanics, it helps to understand what KelpDAO does.
KelpDAO is a liquid restaking protocol that allows users to deposit ETH and receive rsETH — a token representing their restaked position. Restaking means the staked ETH is simultaneously securing Ethereum's base layer while earning additional yield from other networks. It's a capital-efficiency innovation that has attracted billions of dollars in deposits.
rsETH was accepted as collateral on major DeFi lending platforms including Aave, Compound, and Euler, making it deeply integrated into the broader DeFi ecosystem. This is a key reason why the exploit didn't just hurt KelpDAO — it sent shockwaves across the entire sector.
How Did the $292 Million Exploit Happen?
The attack was technically sophisticated and targeted the weakest point in KelpDAO's infrastructure: its cross-chain bridge powered by LayerZero's OFT (Omnichain Fungible Token) standard.
Here is a step-by-step breakdown:
1. Compromising the Verifier Infrastructure Attackers compromised two RPC (Remote Procedure Call) nodes that LayerZero's bridge verifier relied upon to confirm whether cross-chain transactions were legitimate. RPC nodes are the servers that allow software to read and write data on a blockchain.
2. Selective Lying to Stay Invisible The malicious software installed on the compromised nodes was engineered to report fraudulent transaction data only to LayerZero's verifier, while continuing to feed accurate data to every other system querying those same nodes. This "selective deception" kept the attack invisible to LayerZero's own monitoring infrastructure.
3. DDoS to Force Failover Simultaneously, attackers launched a distributed denial-of-service (DDoS) attack on the backup, uncompromised servers — flooding them with junk traffic to make them unreachable. This forced LayerZero's verifier to rely exclusively on the already-compromised nodes.
4. The Fraudulent Transaction With the verifier now receiving only attacker-controlled data, the attackers submitted a fraudulent LayerZero message (nonce 308) to the bridge's OFT adapter. This tricked the contract into releasing real rsETH without a corresponding burn on the source chain — essentially printing unbacked tokens out of thin air.
5. The Drain and Cash Out In one sweep, 116,500 rsETH — approximately 18.5% of the total circulating supply — was drained. The attackers immediately funneled the stolen tokens into DeFi lending protocols like Aave, using them as collateral to borrow over $236 million in WETH and other assets. The stolen funds were then converted to ETH and routed across chains: roughly $178 million on Ethereum mainnet and $100 million onto Arbitrum.
6. The Emergency Pause KelpDAO's emergency multisig froze the protocol's core contracts 46 minutes after the initial drain. Two follow-up attempts — each trying to steal an additional 40,000 rsETH worth roughly $100 million — were blocked. Had the team not acted quickly, total losses could have exceeded $400 million.
KelpDAO vs. LayerZero: Who Is to Blame?
Perhaps as damaging as the exploit itself is the public blame war that has erupted between the two protocols, with serious technical arguments on both sides.
LayerZero's Position
LayerZero published a post-mortem blaming KelpDAO's security configuration. According to LayerZero, KelpDAO chose to operate with a 1-of-1 DVN (Decentralized Verifier Network) setup — meaning a single verifier was responsible for approving cross-chain messages. LayerZero stated it had explicitly warned KelpDAO to adopt a multi-verifier redundancy model.
"A properly hardened configuration would have required consensus across multiple independent DVNs, rendering this attack ineffective even in the event of any single DVN being compromised," LayerZero wrote.
LayerZero has since announced it will no longer sign messages for any application running a 1-of-1 configuration, effectively forcing all single-verifier protocols to migrate.
KelpDAO's Response
KelpDAO disputes this framing entirely. Sources familiar with Kelp's response argue that the compromised verifier was LayerZero's own infrastructure, not a third-party verifier that Kelp independently chose. Kelp claims it followed LayerZero's own quickstart guide and default GitHub configuration — both of which point to a 1/1 single-DVN structure.
Independent security researcher Artem K (@banteg), a developer at Yearn Finance, backed Kelp's position with a technical review. He found that LayerZero's public deployment code uses single-source verification defaults across Ethereum, BSC, Polygon, Arbitrum, and Optimism — adding that roughly 40% of all protocols on LayerZero currently run this same configuration.
Chainlink community manager Zach Rynes summarized the dispute bluntly, accusing LayerZero of "deflecting responsibility" and throwing Kelp under the bus for trusting a setup LayerZero itself promoted.
The Bottom Line
The truth likely sits somewhere between both narratives. A configuration vulnerability created the opening; a state-level adversary exploited it with precision. The more urgent question is: how many other protocols on LayerZero are still running the same 1/1 DVN setup? With 40% exposure across the ecosystem, the answer is unsettling.
Arbitrum's Emergency Freeze: A Historic On-Chain Action
On April 21, 2026, Arbitrum's Security Council took one of the most consequential emergency actions in DeFi governance history. The council froze 30,766 ETH — worth approximately $71 million — that the attacker had routed to Arbitrum One.
The funds were moved from the hacker-controlled address into a frozen intermediary wallet. According to Arbitrum's official statement, the Security Council acted with direct input from law enforcement regarding the exploiter's identity. The frozen funds can only be moved through future Arbitrum DAO governance action.
This intervention is significant for several reasons:
- It demonstrates that Layer 2 governance bodies can act swiftly in a crisis, recovering roughly a quarter of the stolen assets
- It also raises philosophical debates about decentralization: if a council can freeze user funds — even stolen ones — does that introduce unacceptable centralization risk?
- It intensifies the liability dispute between KelpDAO and LayerZero, as the $71 million provides a concrete recovery offset before legal coordination or insurance contributions come into play
Arbitrum stated the method used was "targeted" and had no impact on other users, applications, or the broader chain state.
DeFi Contagion: Aave Faces Up to $230 Million in Bad Debt
The knock-on effects of the exploit moved through DeFi lending markets at alarming speed. Since rsETH was widely accepted as collateral, the sudden collapse of its backing integrity created an artificial bad debt crisis.
Aave Labs and risk service provider LlamaRisk published a detailed incident report on Aave's governance forum outlining two scenarios:
- Best case: Losses are shared across all rsETH holders, causing approximately a 15% depeg, resulting in roughly $124 million in bad debt for Aave.
- Worst case: Losses are isolated to Layer 2 networks, concentrating on Arbitrum and Mantle, resulting in up to $230 million in bad debt.
Aave's total value locked (TVL) dropped from approximately $15 billion to $8.4 billion in just 48 hours — a staggering $6.6 billion collapse. SparkLend and Fluid also moved to freeze rsETH markets.
The ripple effect illustrates a structural vulnerability in DeFi: when a restaking token used as collateral across multiple protocols loses its backing, there is no centralized fail-safe. The market had no clearing mechanism — early, well-connected depositors with automated agents exited first, while retail users were left absorbing losses.
North Korea's Lazarus Group: A 18-Day, $575 Million DeFi Rampage
Both LayerZero and independent blockchain investigators have linked the KelpDAO exploit to North Korea's Lazarus Group, specifically the TraderTraitor subunit.
The same group was attributed to the Drift Protocol exploit on April 1, which drained $285 million through a different attack vector — social engineering of governance signers rather than infrastructure poisoning. Combined, the two attacks represent:
| Attack | Date | Loss | Method |
|---|---|---|---|
| Drift Protocol | April 1, 2026 | $285 million | Social engineering governance |
| KelpDAO | April 18, 2026 | $292 million | RPC node poisoning + DDoS |
| Total | 18 days | $577 million | Two different vectors |
The speed at which Lazarus Group has adapted its tactics — switching from social engineering to infrastructure poisoning in just 17 days — signals a dangerous evolution. DeFi protocols are clearly not hardening their defenses as fast as state-sponsored adversaries are developing new attack playbooks.
Overall, DeFi exploits have topped $775 million in 2026 so far, with KelpDAO and Drift accounting for the bulk of those losses.
What Happens Next?
Several critical developments are still unfolding as of April 21, 2026:
KelpDAO Recovery Fund: Kelp has indicated it is coordinating with ecosystem partners on a recovery fund and is evaluating how to socialize losses across affected users and counterparties.
LayerZero Protocol Migration: LayerZero has announced it will cut off signing for all 1/1 DVN applications, triggering a mandatory security migration for potentially hundreds of protocols currently using its bridge infrastructure.
Arbitrum DAO Governance Vote: The frozen $71 million in ETH must now go through full Arbitrum DAO governance before it can be redistributed, returned, or otherwise acted upon.
Legal and Law Enforcement Coordination: Arbitrum stated its Security Council acted with direct input from law enforcement. This suggests active investigation, though fund recovery from state-sponsored actors remains historically difficult.
Aave Resolution: The outcome for Aave depends largely on how KelpDAO decides to allocate the shortfall — a decision that will affect millions of DeFi users globally.
Key Lessons for the DeFi Ecosystem
The KelpDAO exploit is more than a news story. It is a structural warning for everyone building, investing, or participating in DeFi:
1. Cross-chain bridges remain the weakest link. The vast majority of major DeFi hacks in recent years have targeted bridges. Until multi-verifier redundancy becomes standard practice, every bridge is a potential target.
2. State-sponsored actors are upgrading faster than defenders. North Korea's Lazarus Group is no longer just phishing individuals — it is executing multi-step infrastructure attacks with military-grade precision.
3. Composability amplifies risk. When rsETH is accepted as collateral on Aave, Compound, and Euler simultaneously, a single exploit doesn't just hurt KelpDAO — it destabilizes the entire DeFi lending stack.
4. Governance can act, but speed matters. Arbitrum's 48-hour freeze is impressive, but $221 million in funds remains at large. Faster incident response protocols across DeFi governance bodies are essential.
5. Read your bridge documentation carefully. The argument that 40% of LayerZero protocols are running the same vulnerable configuration is perhaps the most alarming detail of all. Security audits must extend beyond smart contracts to infrastructure defaults.
Conclusion
The KelpDAO $292 million exploit is a watershed moment for DeFi in 2026. It has exposed structural vulnerabilities in cross-chain bridge infrastructure, triggered a governance crisis across Aave and other lending protocols, and demonstrated that state-sponsored hackers are capable of executing sophisticated, multi-layer attacks against decentralized systems.
Arbitrum's decision to freeze $71 million in stolen ETH marks an important moment in blockchain governance — proving that Layer 2 networks can respond decisively to crises. But recovery is far from complete, and the blame war between KelpDAO and LayerZero shows just how murky accountability can become when protocols depend on each other's infrastructure.
For DeFi to mature into a trustworthy global financial layer, these incidents must become the forcing function for mandatory multi-verifier security standards, faster incident response, and more rigorous cross-protocol risk management.
The $577 million drained by one North Korean hacking unit in 18 days is not a fluke. It is a signal that the stakes have permanently risen.
Stay updated with real-time crypto news, DeFi analysis, and blockchain security alerts. Bookmark this page and follow us for the latest developments on the KelpDAO recovery.
Important DisclaimerLegal
All content on Bitiblocky is for educational and informational purposes only and does not constitute financial advice. Always do your own research (DYOR) and consult with a qualified financial advisor before making investment decisions. Cryptocurrency investments carry significant risk, and you should never invest more than you can afford to lose.
Frequently Asked Questions
KelpDAO is a liquid restaking protocol on Ethereum that lets users deposit ETH and receive rsETH tokens. On April 18, 2026, attackers exploited its LayerZero-powered cross-chain bridge and drained approximately $292 million worth of rsETH — the largest DeFi hack of 2026.
Sign in to comment
Join the conversation by signing in